“A security lapse at the privacy-focused social networking app True exposed one of its servers, leading to private user data exposure.”
Tag Archives: Privacy
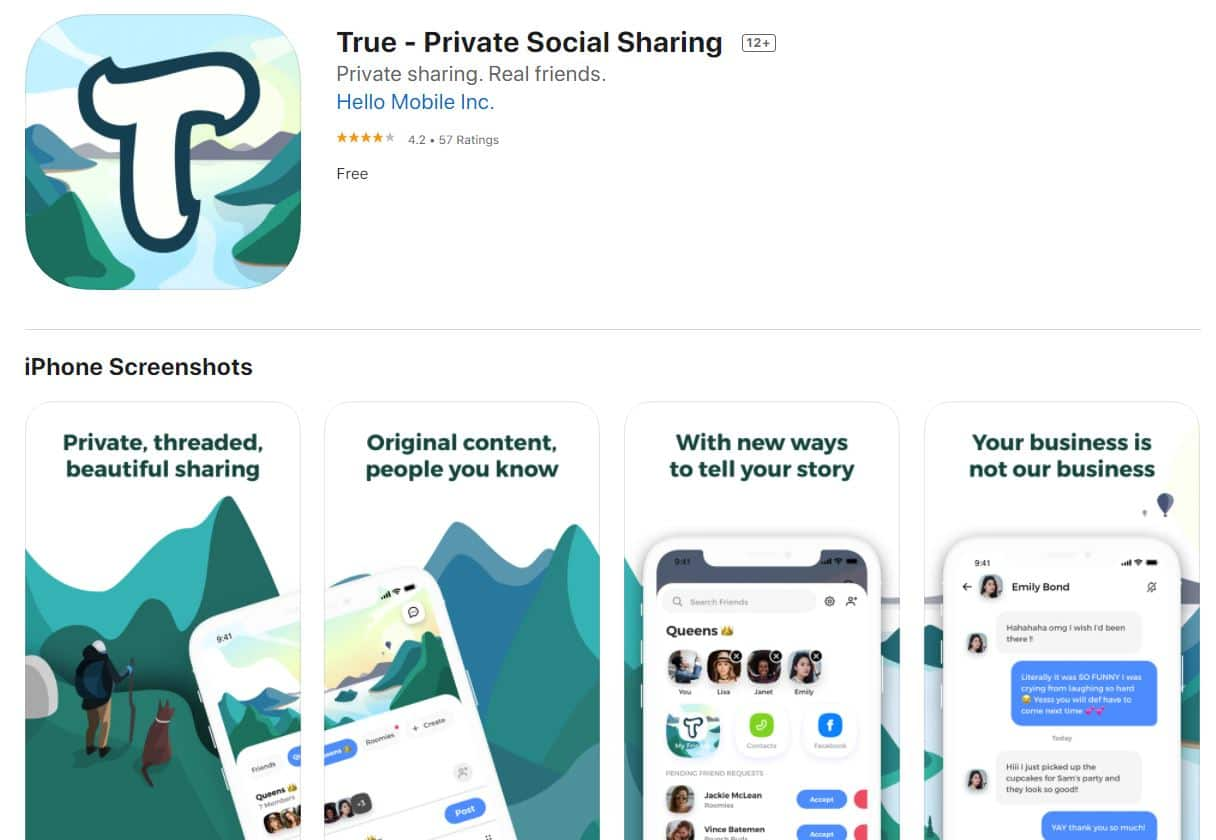
Privacy-focused True social network exposed user data online by https://ift.tt/3mCdoZY
“A security lapse at the privacy-focused social networking app True exposed one of its servers, leading to private user data exposure.”
8 Privacy Features iOS 14 Users Need to Know by https://ift.tt/3iZQ0Dh

“Apple has long provided ways to manage and control your privacy on an iPhone or iPad, but iOS 14 and iPadOS 14 add even more features designed to keep you safe and secure. Here’s how to use them. First, you must update your iPhone or iPad to the latest OS version.”
U.S. Vs. China: who will win the digital currency war? by https://ift.tt/2Fg6Ekt

“The U.S. needs to embrace privacy-focused crypto in order to compete with China’s digital RMB. Co-founder and managing partner at Electric Capital, Avichal Garg, is convinced the only way for the U.S.”
Google Provides Updates on Privacy Sandbox Initiative and Chrome Privacy Updates by https://ift.tt/3iIROjZ
“Google has often been criticized for the various data protection violations that it commits on a regular basis, but with all of that having been said and out of the way it is important to note that the tech giant has also started the Privacy Sandbox initiative which is basically an attempt to make i”
Without encryption, we will lose all privacy. This is our new battleground by https://ift.tt/2qf3Ig6
“In every country of the world, the security of computers keeps the lights on, the shelves stocked, the dams closed, and transportation running.”
Google wins landmark right to be forgotten case by https://ift.tt/2kJ2Gq7
“Europe’s top court has ruled that Google does not have to apply the right to be forgotten globally. The ruling stems from a dispute between Google and France’s privacy regulator CNIL.”
What Is “Reasonable” Privacy? by https://ift.tt/30BgTV6
“If you’ve been following the details of the California Consumer Privacy Act (CCPA), you probably know that the California State Legislature amended the definition of “personal data” to add the word “reasonably” in front of the word “capable” in the phrase “information that identifies”
It’s possible to monetize data while respecting consumer privacy — here’s how by https://ift.tt/2ZX4waf
“Murky policies, tricky wordings, and sneaky assumptions about consent… these are just a few of the shifty tactics being used by companies to learn all about us.”
Why data anonymization doesn’t really guarantee your privacy by https://ift.tt/2zjFWR7
“Data anonymization refers to the process of either encrypting or removing personally identifiable information from data sets, such as names and email addresses.”