
A recent Gartner survey demonstrated just how important digital business has become.
Selected by Galigio via Computer Borders


A recent Gartner survey demonstrated just how important digital business has become.
Selected by Galigio via Computer Borders
Rclone is a command line program written in Go language, used to sync files and directories from different cloud storage providers such as: Amazon Drive, Amazon S3, Backblaze B2, Box, Ceph, DigitalOcean Spaces, Dropbox, FTP, Google Cloud Storage, Google Drive, etc.
Selected by Galigio via Computer Borders

Rclone is a command line program written in Go language, used to sync files and directories from different cloud storage providers such as: Amazon Drive, Amazon S3, Backblaze B2, Box, Ceph, DigitalOcean Spaces, Dropbox, FTP, Google Cloud Storage, Google Drive, etc.
Selected by Galigio via Computer Borders

Rclone is a command line program written in Go language, used to sync files and directories from different cloud storage providers such as: Amazon Drive, Amazon S3, Backblaze B2, Box, Ceph, DigitalOcean Spaces, Dropbox, FTP, Google Cloud Storage, Google Drive, etc.
Selected by Galigio via Computer Borders

Rclone is a command line program written in Go language, used to sync files and directories from different cloud storage providers such as: Amazon Drive, Amazon S3, Backblaze B2, Box, Ceph, DigitalOcean Spaces, Dropbox, FTP, Google Cloud Storage, Google Drive, etc.
Selected by Galigio via Computer Borders

LIBRECON, el congreso internacional de tecnologías abiertas más importante del Sur de Europa, ha anunciado su programa para la edición de este año. En esta ocasión se explotará la aplicación de tecnologías de código abierto en el campo financiero o administración pública.
Selected by Galigio via Computer Borders

I am a Google Drive power user. I depend upon the cloud storage platform daily. And considering I use the Linux operating system as my daily driver, I’ve had to look elsewhere for sync tools (since Google has not opted to create a native Cloud client for Linux).
Selected by Galigio via Computer Borders
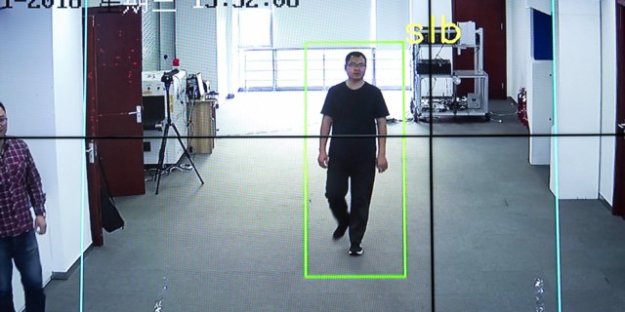
China has rolled out surveillance software in Beijing and Shanghai which authorities say can identify people from their walking style, even with their backs turned and faces hidden.
Selected by Galigio via Computer Borders

China has rolled out surveillance software in Beijing and Shanghai which authorities say can identify people from their walking style, even with their backs turned and faces hidden.
Selected by Galigio via Computer Borders

News briefs for October 23, 2018. Firefox 63.0 was released this morning. With this new version, “users can opt to block third-party tracking cookies or block all trackers and create exceptions for trusted sites that don’t work correctly with content blocking enabled”.
Selected by Galigio via Computer Borders