Something for the Weekend, Sir? Car horns symphonise accompanied by a chorus of yelling cyclists as I shimmy on foot through oncoming traffic….
…Your bot looks cute but it’s easy to crack…
Selected by Galigio via Computer Borders

Something for the Weekend, Sir? Car horns symphonise accompanied by a chorus of yelling cyclists as I shimmy on foot through oncoming traffic….
…Your bot looks cute but it’s easy to crack…
Selected by Galigio via Computer Borders
The fourth industrial age has been driven by a transformative digital revolution. Billions of people worldwide are now inter-connected. We have nearly unlimited access to knowledge, computer processing power, and cloud-based data storage….
…However, the digital revolution also intensifies fundamental tensions regarding how best to reconcile the privacy of our citizens with our desire for personal safety; pitting at times national security against our own individual liberties, and balancing the interests of a company’s customers against its civic responsibilities…
…Unfortunately, many laws governing data sharing and privacy were created decades ago and are woefully outdated. For example…
from https://is.gd/GH23I4
Selected by Galigio via Computer Borders
Opera today launched version 50 of its desktop browser. Sadly, this release doesn’t come with a cake to celebrate this milestone (not even a tiny cupcake), but the newest release does include a new feature that makes sure that nobody can mine crytocurrencies in your browser.
In Opera, this new cryptojacking feature is automatically enabled when you turn on the browser’s ad blocking tool.
from https://is.gd/kA4S26
Selected by Galigio via Computer Borders
For years, TrueCrypt was the encryption tool of choice for Linux users. It worked well, and it did everything you could ever want. Then one day, the project was discontinued. Ever since then, Linux users have been scrambling to find an encryption tool that works as well.
For most, the best tool to use is VeraCrypt. The main reason that VeraCrypt stands out from the rest of the new encryption tools is that it is a “fork” from the old TrueCrypt code. This means if you’ve used TrueCrypt for years but want something that is actively maintained, you can install VeraCrypt on Linux and everything will continue to work.
from https://is.gd/HFNBWZ
Selected by Galigio via Computer Borders
The five statements below are the causes behind a lot of computer security risk and exploits. If you understand them well enough today, you will be ahead of your peers.
from https://is.gd/4zaJnw
Selected by Galigio via Computer Borders
The effect of geopolitics on cybersecurity can be seen daily – from Chinese cyber espionage to Russian attacks on the Ukraine and North Korea’s financially-motivated attacks against SWIFT and Bitcoins – and, of course, Russian interference in western elections and notably the US 2016 presidential election.
The primary cause is political mistrust between different geopolitical regions combined with the emergence of cyberspace as a de facto theater of war.
Selected by Galigio via Computer Borders
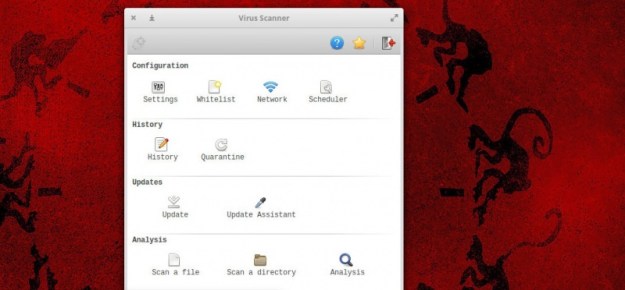
Wait, Linux needs antivirus and anti-malware solutions? I thought it was immune to such things. Perhaps a bit of clarification is necessary here. First and foremost, no operating system is 100 percent immune to attack. Whether a machine is online or offline, it can fall victim to malicious code.
Although Linux is less prone to such attacks than, say, Windows, there is no absolute when it comes to security. I have witnessed, first hand, Linux servers hit by rootkits that were so nasty, the only solution was to reinstall and hope the data backup was current. I’ve been a victim of a (very brief) hacker getting onto my desktop, because I accidentally left desktop sharing running (that was certainly an eye opener). The lesson? Even Linux can be vulnerable.
from https://is.gd/VLyo98
Selected by Galigio via Computer Borders
Are you worried that your Linux computer may be infected with malware? Have you ever checked? While Linux systems tend to be less susceptible to malware than Windows, they can still be infected. Many times they’re less obviously compromised, too.
There are a handful of excellent open-source tools to help you check if your Linux system has been the victim of malware. While no software is perfect, these three have a solid reputation and can be trusted to find most known threats.
from https://is.gd/Mcj0vO
Selected by Galigio via Computer Borders
Firewalls represent the technological gateways into and out of companies, as well as serving to compartmentalize internal systems and networks to segregate them from one another.
Network traffic flowing through, or blocked by, firewalls does so based upon specific permissions intended to secure systems, services and users from unauthorized access or malicious threats.
A properly maintained firewall is one of the keys to business and operational success.
from https://is.gd/DwBX47
Selected by Galigio via Computer Borders
Google runs lots of different systems, and they all store data about you. There’s the search engine itself, of course, which knows what you’ve been looking for on the web. Then there’s Youtube, Blogger, Calendar, your Google Drive, Hangouts, Gmail and more.
If you want to download a copy of all the data about you that’s held on Google’s servers, it’s actually surprisingly easy.
from https://is.gd/jzuEd0
Selected by Galigio via Computer Borders