Today utilizing an external drive is the most often used strategy for having an efficient backup storage. On the other hand, the people who contemplate utilizing cloud computing for this purpose often wonder if the technology is worth the attempt.
Users of the system ensure that there’s no reasons why anyone should keep from utilizing this system as it guarantees numerous additional benefits as when compared to the traditional methods. The truth that you’ve to fork out a “minuscule” amount of cash on a -monthly- basis for the use of cloud data storage is one motive behind prospective users to be careful.

Courtesy of https://www.surdoc.com
The following benefits of the technology are cause enough to make sure that this expense property is truly worth it.
Extensive storage space: The most elementary advantage of utilizing the cloud is that you can store any quantity of information, which is difficult when using drives. The system is very simple to utilize as the account is created within a few minutes, as opposed to the effort and time spent on going searching for an additional drive.
No Physical existence: Once you have saved your data on the cloud, it becomes the obligation of the supplier to worry about its preservation. Rather than purchasing and saving these numerous added drives, one only has to stay attached to the web in order to access the stored information.
Convenience of automatic back-up: The consumers of cloud computing do not have to trouble making sure that they have related the external drive to their computers and that they take back-ups occasionally. The options on the cloud system may be altered as per the user’s setting as to whether the back-up must be taken several times in one day or once each day. The only obvious prerequisite for the system to be copied is the internet must be related and anything else is looked after.
Easy restoration: In usual conditions, locating and repairing a hard disk drive from backed up information is a long and troublesome process which calls for the providers of the pc technician. The cloud consumers are spared from such an annoyance as this restoration procedure is made quick and simple. If at all the users however have questions about managing this on their very own, they could always seek help from the companies plus they’ll be more than happy to oblige.

Courtesy of http://labs.sogeti.com
It is important to understand the dangers involved when transferring your business into the cloud before contemplating cloud computing technology. You should perform a risk assessment procedure before any control is handed over to a service provider.
First of all you should deeply understand what is the real privacy protection offered by the Cloud Provider. Nowadays the best (more secure and/or more respectful of your privacy) Hosting – Cloud Providers are redeploying their storage servers from USA to Switzerland. This happens because in general Swiss has a better privacy protection and it is outside the European Union and United States Laws. This means that in Swiss, disclosure order/warrant have less possibilities to have effects than in US or EU if they have not a very good legal motivation.
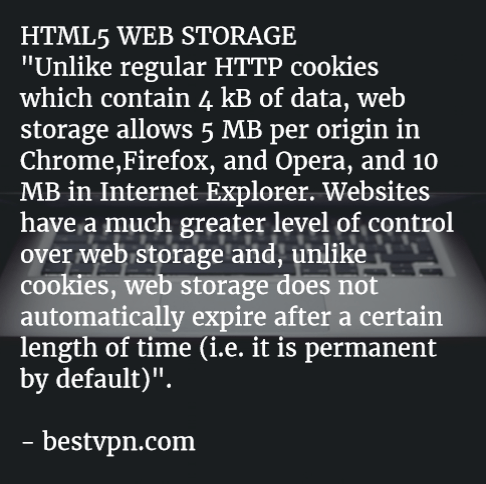
More in general, it is possible to affirm that any location of the Cloud Provider could be good if you understand the local privacy legislation before you use its services. Moreover the Cloud Providers have to guarantee an encrypted storage without detaining any key that can, directly or indirectly, decrypt the information you save or use through its servers. Consequently all the data transmission have to use https protocols with a recommended minimum of 1024 bits encryption. On my side I privilege nothing that offers less than a 2048 bits https protection.
Usually you can have a good representation about the security of the services offered and the legal legislation that will affect your Cloud Service contract if you read carefully the EULA.
For this reason, before committing, you should inquire which privacy and security laws will apply to the information and where your information will be saved. In case the information will be saved outside of your Country, you will also need to be informed as to the laws and regulation demands in that specific geographic place.
Moreover you have to understand if the Cloud Provider that you are choosing to support your business, is really able to guarantee an adequate service level. Don’t be worried to send inquires if the information provided in their Service Level Agreement don’t solve tour doubts or you think that the provided services could not match with your needs in future because they seems not enough flexible.
Anyway, try to prefer a Cloud Service Provider that has an effective Customer Support Service that can promptly (24/7/365) solve your problems. Cloud Service reseller are (sometimes) cheaper but they could not be the best choice for your business technical needs.
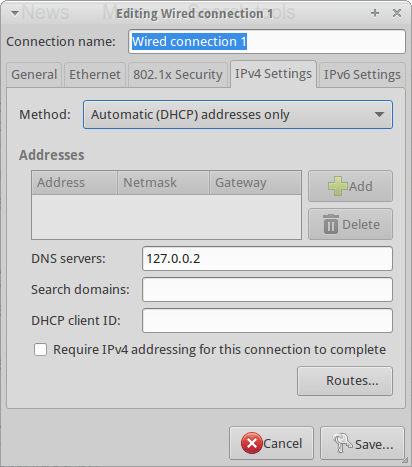
Courtesy of webopedia.com
Last but not least, don’t underestimate the security holes represented by the human factor. You have to offer the right level of training to your employees and colleagues because just a single mistake by them, can be transformed, by an hacker or a competitor, in a potential debacle for all your Cloud System. Invest in learning courses about Cloud risks for all your employees and colleagues, let them understand what are the potential risks of using Cloud Services. Don’t be afraid to introduce “difficult” technical concept (as e.g. man-in-the-middle attacks, different encryption systems, social engineering tactics, the importance of digital signs, etc..) to them.
For this reason, in order to reach a better security level, configure all the electronic devices (common: tablets, smartphones, laptops & uncommon and often more dangerous: all the hardware with an embedded OS especially if they are able to communicate data through Internet or your phone provider) in order that they use your VPN by default. If you will be able to secure all the transmission through your reliable VPN you could have solved at least the 40-50% of the potential mistakes that are normally made by your employees or colleagues.